Centralizing Windows Events using a Collector Initiated Subscription
So it seems like the best way to go about centralizing Windows Events in an Enterprise is to use GPO, but if you can't or don't want to involve Active Directory GPOs, here's a guide on using one server to go out and collect Windows Events from other servers on your domain.
Things you'll need: Windows Server 2012 or 2008 R2, the appropriate ports open on your firewall if you're running one, access to a Domain Admin service account or the ability to add a Machine account to a local group on each of the servers you're collecting from.
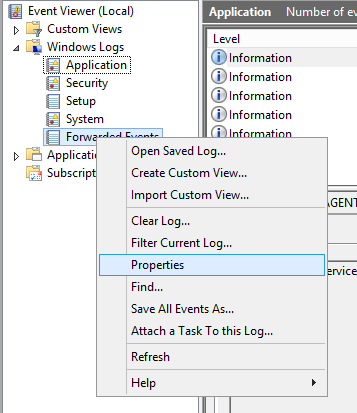
So here's how to setup a Windows 2012 or 2008 R2 Server as the Event Collection Server: first, open up Event Viewer, right click on Forwarded Events and click Properties.
Note that Application, Security and System look a bit different than the others. I believe that's because they are considered Classic Windows Events. Classic Windows Events can be easily parsed in PowerShell using Get-EventLog and WMI's Win32_NTEventLogFile but the newer Event Types are a bit trickier.
The first thing you see in the Forwarded Events property tab is this:

Note the location of the ForwardedEvents.evtx file as it may come in handy for future troubleshooting or archiving. Next, click on the "Subscriptions" tab, then Create.

Now here, I will create just one generic Subscription to capture all Critical and error events. You can create multiple subscriptions for differing criteria and just send all of them to the Forwarded Events log. So select "Collector Initiated" and "Select Computers." Unfortunately, you have to add each server one by one when using the GUI. If you want to add in bulk, you'll likely have to do it using Group Policy and Source Initiation. I haven't found a way to do it in PowerShell yet.
Click Select Events and select what you'd like. My servers are super verbose, and I really only care about Criticals and Errors so I select those two Event Levels, and then By log: Application and System.

Once you're done with your Event selections, click on Advanced to modify the account you'd like to use as the collector (in my lab, I used a Domain Admin account).

If you use a Machine account or a non-admin, you'll have to go to each of the forwarding servers and add the Computer or User AD account to Event Log Readers.
Here, you can also configure the Event Delivery Optimization. I left it default for now, though later I do plan to explore delivering Events over HTTPS. Click OK until you're back at Event Viewer. Wait a few minutes and the Events should start coming in. In my experience, for each new computer I setup, I'll get one Information event from the Microsoft-Windows-EventForwarder provider. The event itself is kind of useless, saying "the description for Event 111 cannot be found." but I've learned to accept it's the Event Forwarding confirming there's a new computer in the subscription.
When things get going, your Windows Forwarding collection should look something like this:
In this screenshot, I've highlighted Attach Task to Event which allows you to run a program or send an email when the event occurs. Pretty cool.
If you need additional help, Microsoft has a Quick and Dirty Large Scale Eventing for Windows guide that is good for troubleshooting.