Joining Ubuntu to an Active Directory Domain
Back in 2009, I did a whole lot of messing around with Linux and Active Directory integration, primarily for Apache. Now that Linux is coming to Windows, I figured I'd brush up on my Linux and Windows Integrated Authentication skills to work with Ubuntu, too.
Clients and Servers
Since 2009, it seems that a couple things have changed in the client realm. In particular, winbind fell out of favor to Likewise Open (which I used to <3) which was bought by BeyondTrust and turned into PowerBroker Open. But that's since fallen out of favor to the SSSD or "System Security Services Daemon". SSSD seems pretty cool but everyone hates its name and assumes that its name is keeping it from greater adoption.
Sometimes when researching SSSD, you'll come across a few mentions of FreeIPA which is similar to Active Directory, OpenLDAP, and ApacheDS. Oh, and I recently found out that Samba4 allows Linux servers to join Active Directory as Domain Controllers (!!) but I can't tell if it can be a forest of its own (reddit review here).
There are other players I'm leaving out but after a bit of casual research, no others seem to stand out. Ultimately, while there are a number of ways to setup AD/Linux authentication with Ubuntu, it appears that SSSD is the current way to go. Let's go ahead and set that up.
Before We Begin
There's an official Ubuntu guide for SSSD and Active Directory, but this one is slimmed down. If you have any issues, you can comment here or reference some of the solutions they offer. First, some assumptions.
- Fresh install of Ubuntu 15.10 Server
- DNS is set to AD's DNS servers
- The Active Directory domain is base.local
- The test user is base\adadmin, which has domain admin privs on AD
If you're behind a proxy, apt-get and curl/wget/etc won't work out of the box. Here's how to add some proxy variables (kinda like Internet Properties -> Connections -> LAN settings -> Proxy Server) so that you can use these tools.
Also, you're going to need to make sure that your time is set properly. Kerberos is heavily dependent on time, and will break if your computer is more than 5 minutes skewed from the AD domain.
1# Install required packages (ntp service keeps your clock on time)
2sudo apt-get -y install ntp ntpdate
3
4# To add your DC to the time server list, edit /etc/ntp.conf, otherwise this should work
5sudo service ntp stop
6sudo ntpdate -s ntp.ubuntu.org
7sudo service ntp start
Joining the domain
Joining an Active Directory in Ubuntu isn't quite as easy as SUSE, but it's still decently straight-forward.
- Install required packages
- Create and modify sssd.conf
- Modify smb.conf
- Restart services
- Join domain
First, installed the required package using apt-get. I also recommend command-not-found and mlocate, which help you with finding files.
Note, in this tutorial, I use vi. I used to use pico, which became nano, but found that vi could be found across all distributions by default. vi or "vim" can be intimidating, but honestly, I only know about 5 commands and it gets me by. Here's a nice tutorial on Learning vi progressively.
1sudo apt-get install krb5-user samba sssd
Next, setup SSSD by creating the file, setting the owner, and changing its permissions
1# sssd.conf doesn't exist by default
2sudo touch /etc/sssd/sssd.conf
3sudo chown root:root /etc/sssd/sssd.conf
4sudo chmod 600 /etc/sssd/sssd.conf
5
6sudo vi /etc/sssd/sssd.conf
7
8[sssd]
9services = nss, pam
10config\_file\_version = 2
11domains = BASE.LOCAL
12
13[domain/BASE.LOCAL]
14id_provider = ad
15override_homedir = /home/%d/%u
16access_provider = simple
17simple_allow_users = [email protected],[email protected]
18simple_allow_groups = linux-admin,linux-users
Note that this config only allows 2 users and 2 groups to gain access. If you remove the last 2 lines, anyone can login. There are a few ways to restrict access but it looks like this is the simplest way.
Next, sudo vi /etc/samba/smb.conf and replace the line workgroup = WORKGROUP with the following:
1workgroup = BASE
2client signing = yes
3client use spnego = yes
4kerberos method = secrets and keytab
5realm = BASE.LOCAL
6security = ads
Time to restart services and join the domain! Here's a screenshot of my Ubuntu server "ubuntunew" joining my domain, base.local:
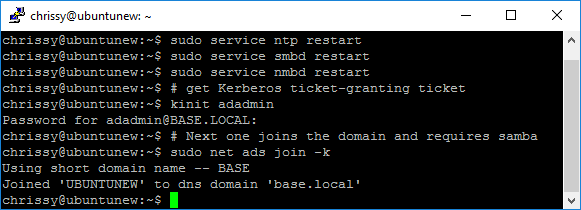
It's just these commands, nothing scary:
1# restart services
2sudo service smbd restart
3sudo service nmbd restart
4# get Kerberos ticket-granting ticket
5kinit adadmin
6# Next one joins the domain and requires samba
7sudo net ads join -k
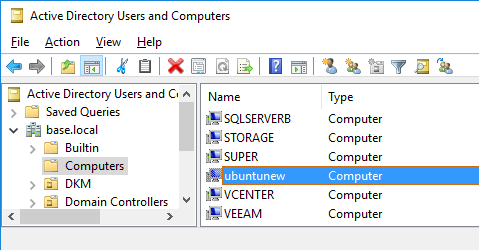
If you have permissions to add computers to the domain and everything went well, then you should now be able to see your Ubuntu server in Active Directory!
Now that everything is setup all nice, start SSSD to do some caching and interception that makes things much smoother somehow.
1sudo service sssd start
Troubleshooting
If you're having an issue joining the domain with the error message "Failed to join domain: failed to lookup DC info for domain 'BASE.LOCAL' over rpc: An internal error occurred" you can specify the exact domain controller you want to contact (h/t Florent Appointaire).
1sudo net ads join -S dc.base.local
If you're getting the error "failed to lookup dc info for domain base rpc undetermined error", you may have a stale DC. Consider following applicable portions of this tutorial by Microsoft (h/t Rob Sewell)
Login as Windows user
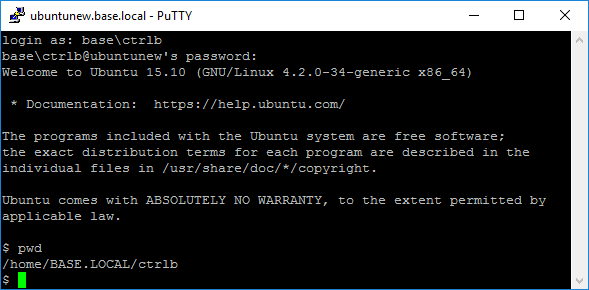
If you'd like to login to the machine as a windows user, as opposed to just grabbing a ticket using kinit, you can either login via SSH or by using su or "substitute user".
Here's an example of me using su. First, I logged in to the Linux server as a regular user, then I login as my own Active Directory account "base\ctrlb" by issuing the command su ctrlb. An alternative way is su base\\ctrlb. That extra backslash is intentional, it escapes the second backslash.

Alternatively, you can ssh in directly with ssh or PuTTY.
And that's it! Want to see this all in one shot? Check out the gist.